Kaspersky Incident Response
Managing the aftermath of a security breach
![]()
Overview
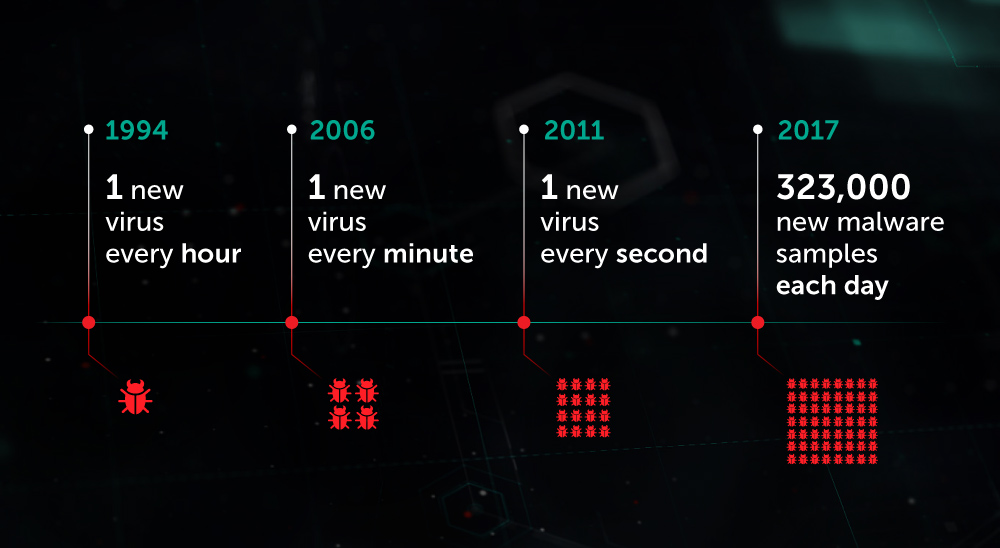
It’s becoming increasingly difficult to prevent information security incidents. But, while it may not always be possible to halt an attack before it penetrates your security perimeter, it’s absolutely within our power to limit the resultant damage and to prevent the attack from spreading. The full weight of Kaspersky Lab’s global expertise can be brought to bear on the resolution of your security incident.
![]()
Incident Response
Covering the entire incident investigation cycle to completely eliminate the threat to your organization
![]()
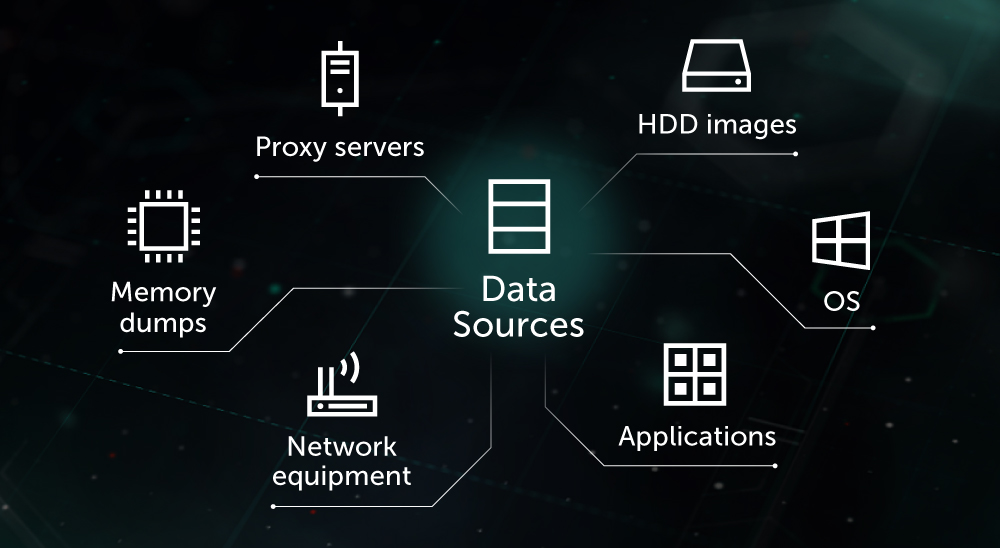
Digital Forensics
Analysis of digital evidence related to a cybercrime, revealing a complete picture of an incident
![]()
Malware Analysis
Providing you with exhaustive information about the behavior and functionality of specific malware files
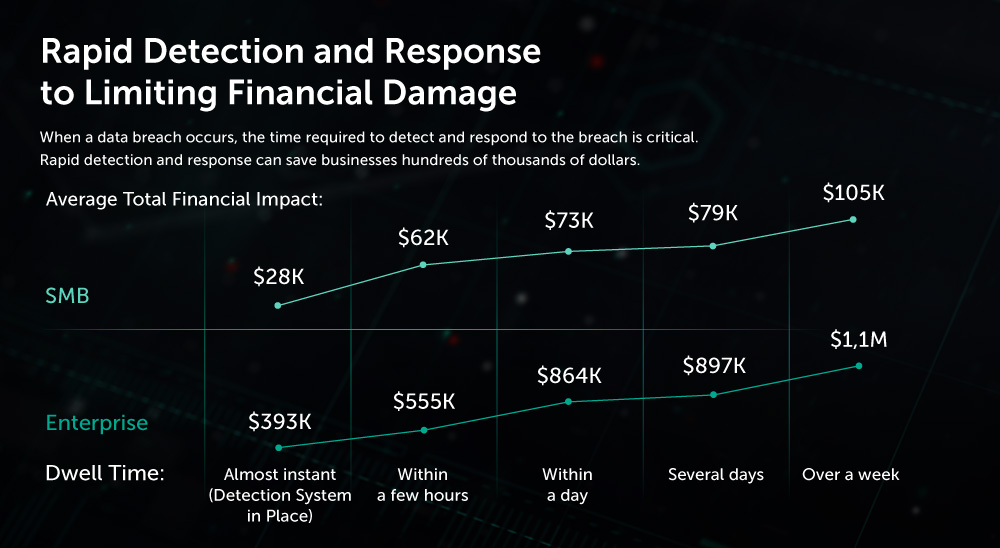
The importance of incident response
While your infosec team works hard to ensure that every network component is protected, a single vulnerability could open the door to intruders, giving them access to your information systems.
Anything can be targeted. If a system gets hacked, it is vital to establish how it was compromised in order to draw up an attack mitigation plan and prevent such attacks in the future. The incident response service achieves these goals.
How the service works
An incident constitutes a breach or the threat of a breach of computer security policies, acceptable use policies and / or standard security practices.
Incident response — obtains a detailed picture of the incident. The service covers the full incident investigation and response cycle: from early incident response and evidence collection to identifying additional traces of hacking and preparing an attack mitigation plan.
The Risk
While your specialists work hard to ensure the security of every network component, a single vulnerability can offer an open door to any cybercriminal intent on gaining control over your information systems. No one is immune: however effective your security controls, you can become a victim.
Suitable for
This solution is particularly well suited to addressing the security requirements, concerns and constraints of these enterprise sectors.
- Enterprise
- Financial Services
- Managed Security Service Providers
- Critical Infrastructure
Pricing Notes:
- Pricing and product availability subject to change without notice.